Apple To Issue iOS And MacOS Software Updates To Fix Exploit In FaceTime Group Call Feature
NEWS: 01.30.19- “Can you hear me now?”, the famous tagline once used by Verizon Wireless, is a question not being asked by unsuspecting iPhone users with a newly discovered exploit in the smartphone’s software that allows another user who initiates a FaceTime group call — by including their own phone number in the chat — to eavesdrop on and even see (through the front-facing camera) the recipient without them knowing it or even accepting / dismissing the request and Apple — which has been made aware of this security risk — will be issuing a forthcoming software update to iOS in order to address and fix the issue.
On Monday evening Apple, through a spokesperson, said in an official statement:
“The company is aware of this issue and we have identified a fix that will be released in a software update later this week.”
The security risk is only found with iPhone users running iOS 12.1 or later and also affects other iOS devices including the iPad and iPod touch. In addition, Mac users running MacOS Mojave version 10.14.1 or later are affected too.
The exploit was first reported Monday afternoon by the website 9to5 Mac which outlined the exact steps to recreate the flaw to anyone interested in seeing it for themselves but apparently was unnecessary as writer Benjamin Mayo mentioned in the article, the exploit was being spread virally by iPHone users all over social media.
On Tuesday, the story had made the rounds through almost every major news media outlet from CNN to ABC News.
The day before, writer Eli Blumenthal of the newspaper publication USA Today wrote in his article the following:
“USA Today was able to recreate the bug on multiple iPhones running versions of iOS 12.1 on devices ranging from the iPhone 6 to the iPhone XR. We were also able to recreate it on a MacBook Pro, allowing the iPhone to listen in to the Mac running the latest version of MacOS Mojave. We were not able to test the bug on an iPad running iOS 12.1 but those who have Apple’s tablets may want to exercise caution until a fix arrives.”
Blumenthal also reported that regular one-on-one FaceTime calls did not appear to be affected by the exploit.
In an article by tech reporter Nicole Nguyen of the website BuzzFeed News, an update Tuesday — a day after her original report — added additional details including the handle of the Twitter user whose team had originally discovered the exploit on January 20. According to her, three days later, a video demonstrating the flaw was sent to Apple by the team. It was only on Monday when the team learned that the specific issue involved the FaceTime group call feature.
This revelation would suggest that Apple possibly had been aware of the security risk to iOS for a week before the news broke on Monday.
The post by Twitter user MGT7500 is as follows:
“My team found a major security flaw in Apple’s new iOS. He can listen in to your iPhone/iPad without your approval. I have submitted video bug report to @AppleSupport …waiting to hear back to provide details. Scary stuff!”
According to writer Brian Barrett of Wired magazine, it was the Twitter user’s 14-year old son who first discovered the vulnerability when he tried to setup a group chat with friends for a round of the popular video game “Fortnight.” Barrett also reported that the mother received no replies from Apple for a week after reporting the issue to the company and making numerous inquiries about the discovery..
Macworld magazine staff writer Michael Simon credited reporter Mark Gurman, who covers technology for Bloomberg as the person who pointed out the following and wrote:
“The irony of all this is that the bug was discovered on Data Privacy Day which was marked with a tweet by CEO Tim Cook saying the dangers are real and the consequences are too important. It’s hard to argue with those words, especially when it’s your own iPhone that poses the danger.”
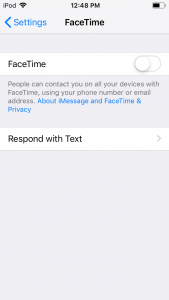
Though Apple has since disabled the ability to make a FaceTime group call as a temporary way to address the issue, in the meantime, as a simple precautionary measure and for people’s peace of mind, until software updates to iOS — and MacOS — are released, iPhone and other iOS device users can turn the feature off in the Settings app (and by going to preferences in the FaceTime application on your Mac).
